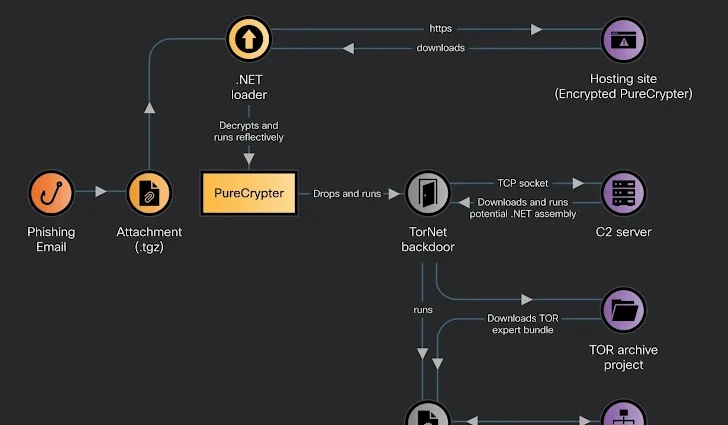
PureCrypter Unleashes New Wave of Sophisticated Cyberattacks
PureCrypter Deploys Agent Tesla and New TorNet Backdoor in Ongoing Cyberattacks A new wave of cyberattacks has emerged, driven by the notorious malware distributor PureCrypter, which is using a combination of Agent Tesla and the newly discovered TorNet backdoor to target organizations and individuals. This ongoing campaign is a clearContinue Reading